Key Takeaways
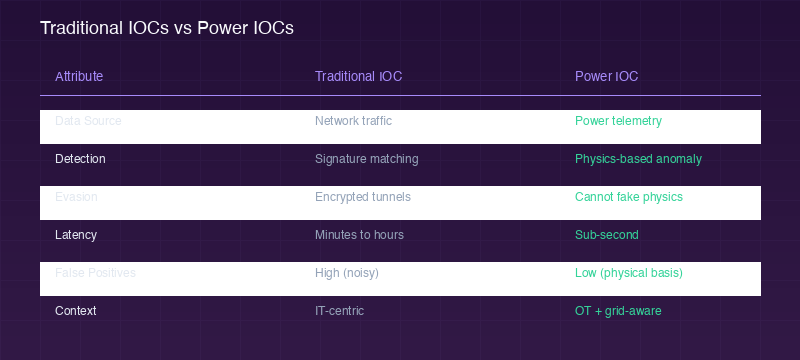
- Power IOCs are a new category of threat detection specific to operational technology and energy systems
- Physics-based detection cannot be evaded by encrypted tunnels or credential theft
- Sub-second detection latency compared to minutes or hours with traditional IOCs
- DERSec Sentry is the first platform to operationalize Power IOCs for DER security
A New Category of Threat Detection
In traditional cybersecurity, Indicators of Compromise (IOCs) are artifacts — IP addresses, file hashes, domain names — that signal malicious activity on a network. They have served enterprise IT well for decades. But in the world of operational technology (OT) and distributed energy resources, traditional IOCs fall short.
The fundamental problem: attackers targeting DER infrastructure don’t need to use malware, known-bad IPs, or suspicious domains. They can compromise a solar inverter by sending perfectly valid IEEE 2030.5 commands that happen to destabilize the grid. The commands look legitimate. The network traffic looks clean. Traditional IOCs see nothing.
Detection Latency
Fewer False Positives
Evasion via Encryption
What Makes Power IOCs Different
Power Indicators of Compromise (Power IOCs) represent a fundamentally different approach. Instead of looking at network artifacts, Power IOCs analyze the physics of the energy system itself.
Consider a compromised solar inverter. An attacker commands it to inject reactive power at maximum capacity during peak demand. From a network perspective, the command is properly authenticated, encrypted with TLS, and follows the IEEE 2030.5 specification exactly. No traditional IOC will flag it.
But the physics tell a different story. The power factor drops unexpectedly. The voltage at the point of interconnection deviates from the expected profile. The reactive power output doesn’t match the grid operator’s dispatch signal. These are Power IOCs — physical anomalies that reveal cyber-physical attacks.
You cannot fake physics. An attacker can steal credentials, encrypt their traffic, and use zero-day exploits. But they cannot change the laws of thermodynamics or make electrons behave in ways that violate power system equations.
The Detection Pipeline
DERSec Sentry implements a five-stage pipeline for Power IOC detection, from raw telemetry to actionable alerts:
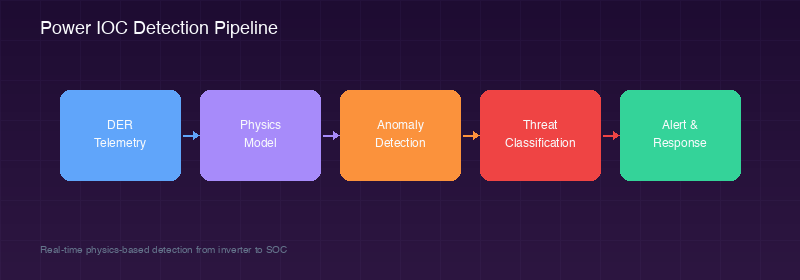
How the Pipeline Works
Stage 1 — DER Telemetry: Raw measurements from inverters, batteries, and EV chargers (voltage, current, power factor, frequency). Stage 2 — Physics Model: Expected behavior computed from grid conditions, weather data, and dispatch signals. Stage 3 — Anomaly Detection: Statistical comparison of observed vs. expected behavior. Stage 4 — Threat Classification: Machine learning categorizes anomalies as benign, suspicious, or hostile. Stage 5 — Alert & Response: Actionable intelligence delivered to SOC with recommended containment actions.
Categories of Power IOCs
DERSec Sentry monitors for several categories of Power IOCs across the DER fleet:
- Power Factor Anomalies — Unexpected reactive power injection or absorption
- Voltage Deviations — Voltage excursions at the point of interconnection
- Frequency Response Violations — Devices not following frequency-watt response curves
- Ramp Rate Anomalies — Power output changes faster than physics or firmware allow
- Dispatch Divergence — Device behavior deviating from grid operator commands
- Telemetry Spoofing — Reported values that violate conservation of energy equations
Critical Consideration
Power IOCs are not a replacement for traditional network security. They are a complementary layer that detects attacks invisible to IT-centric tools. A comprehensive DER security strategy requires both network monitoring and physics-based detection.
Getting Started
Power IOCs are built into every DERSec Sentry deployment. No additional configuration is required — the physics models are automatically calibrated during the initial learning period.
Learn more about DERSec Sentry and how Power IOCs can protect your DER fleet from cyber-physical attacks.
